Extensions – Useful but Risky
Browser extensions are great. They’re like mini-programs that add features to web browsers. There are many that are tremendously useful: remote desktop add-ons, ad blockers, price comparison tools, add-ons that transform the color schemes and layouts of web pages, and many more. And many of these incredible extensions are completely free to use.
And sure, there are also plenty of extensions that are not worth using: buggy, unfinished, outdated, or lacking in features. But there are some that are even worse: dangerous.
There are spyware, adware, and miners. They log your data, which can include personal information, and share it with third parties. They inject ads into the pages that you open. And they even display ads on your home page. And they intercept your web browsing to redirect you to partner websites so that they can display advertisements.
Extensions promise to make your browsing safer and more private – but instead, they spy on you and open malicious sites for you.
For instance, fake cryptowallet extensions were used to steal users’ credentials. People would use these extensions to log in to their online wallets, thus revealing sensitive information to malicious actors. Stolen credentials could then be used to rob the victims.
Google and other browser developers work constantly to remove malicious extensions, such as ad injectors, from their stores. But the battle is never over. Malicious actors continue to upload bad extensions.
Recognize Unsafe Browser Extensions
So, how to recognize a browser hijacker that’s harmful? How to avoid installing them?
We’ve already talked about this before in the post How to avoid browser hijacking. Be careful while installing free programs. And when you notice something wrong with your browser, check it over without delay.
But it’s best to avoid browser hijackers before they can start causing problems. And now that the landscape of online threats has changed a bit, we need to update the advice.
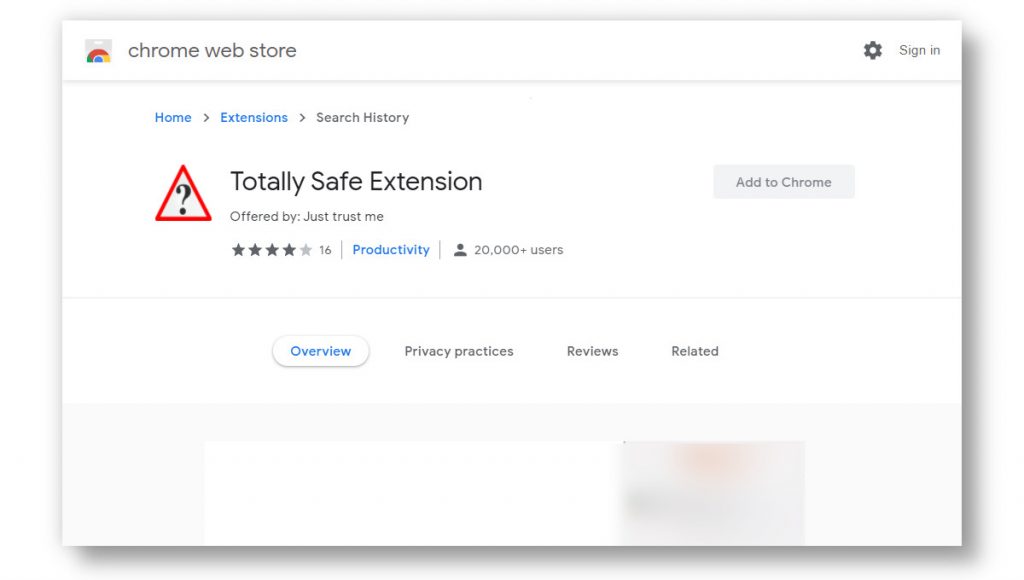
When you find yourself on the Chrome Web Store or another add-on store, be patient and keep a level head. Pay attention to these extension features:
- Who is the developer of the extension? Is it a trustworthy company? What else have they released?
If you can’t find out who the developer is, that’s a red flag. - What does the privacy policy say? Are you comfortable with the data that is collected?
- What are the reviews? Be suspicious of fake reviews, such as large numbers of extremely short reviews all posted within a couple of days.
- What permissions does the extension ask? If it wants to read your data on all sites that you visit, do you believe that it has a good justification?
None of this advice is perfect. Extensions with extremely modest permissions can still interfere with your internet search. Genuinely good extensions can suddenly release malicious features. And truly malicious extensions can be disguised as coming from a reputable and trustworthy developer.
Still, being careful will help you avoid the vast majority of browser infections and stay safe on the internet.